IOTA Reclaim Identification Verification Process
Update: The latest updates on how to claim your tokens can be found in this FAQ.
An important update to our community and partners
As most members of the IOTA Community know, in October of 2017 a bug was found in the early normalization code for IOTA transaction signature bundles. The details are highly technical, but the intrepid may check out Eric Hop’s excellent blog post on the IOTA signing process to fully understand them. For the less technically-minded, the upshot is that the bug put the IOTA tokens of certain users at risk by partially revealing a portion of the private key generated for specific addresses. This would have made it easier for malicious attackers to potentially “brute force” hack the remainder of those addresses’ private keys and thereby steal the tokens.
The IOTA open source community quickly came together to develop a patch for this bug. Over the course of three days, the coordinator was shut down (to make it more difficult for any brute force attacks to be confirmed), a patch was deployed, and the community of full node operators reached a consensus to carry out an emergency snapshot to prevent the loss of any user tokens.
In the current version of the Tangle’s deployment, snapshots are carried out on a periodic basis to prune the ledger and make it faster by removing all zero-balance addresses. (A general explanation of snapshots in IOTA can be found on the Hello IOTA Forum.) In this case, however, the community took the unprecedented decision to carry out a snapshot that would essentially wipe out the effects of the bug by sweeping the at-risk tokens to new, safe addresses from which they could be returned to the original owners via a reclaim process.
It is important to stress that this step was not taken lightly and was not carried out by any single individual or organization. Rather, the idea was proposed and debated by the community of IOTA developers and then put to a vote by the entire network of IOTA full-node operators worldwide. Motivated by the belief that rescuing the at-risk tokens was the right thing to do, the full node operators — some of whom remain anonymous — unanimously opted to validate the snapshot and rescue the at-risk tokens. The rescued tokens were then made subject to areclaim process which was announced in an IOTA blog post on 25 October 2017. A further update on the reclaim process was then provided on 9 November 2017.
Many users have already received their tokens back through the reclaim process, while others are still waiting (more on that in a minute!).
The fact that IOTA is a public, permissionless distributed ledger means that users can create wallets, obtain IOTA tokens, and send and receive transactions via the Tangle without ever having to notify or share their personal details with anyone. Permissionless innovation is one of the core features of IOTA’s design. It is a bedrock commitment which the IOTA community shares in common with many of the leading open source projects in the blockchain and distributed ledger space. For this reason, neither the IOTA Foundation nor anyone else who contributes to or uses IOTA has any way of knowing — on the basis of the protocol alone — who owns which individual IOTA addresses.
This privacy-by-default design fosters permissionless innovation within the IOTA Ecosystem, and this is something we are very proud of. But it also poses special challenges when it comes to completing the token reclaim process. In certain cases (around 200), more than one person submitted a reclaim for the same IOTA address. This may have happened inadvertently. For example, a user attempting to reclaim his or her tokens might have submitted a reclaim request asking to have the tokens sent to new Address A, then later submitted a second reclaim request asking to have the same tokens sent to new Address B. Perhaps the user did this because s/he had meanwhile used Address A for something else (and everyone knows you should never use an IOTA address more than once!). Or perhaps the user wasn’t sure if the first request had successfully been recorded, so s/he submitted a second one out of an abundance of caution. Our working assumption is that many of the double reclaims amount to simple innocent mistakes of this sort.
We cannot rule out, however, that some duplicate reclaims might represent attempts by thieves to steal the tokens of other legitimate users. Since the bundle bug revealed portions of the affected users’ private keys, it is theoretically possible that a savvy hacker might have been able to brute-force the remainder of the private key and submitted a reclaim for someone else’s tokens. Unfortunately, without obtaining the further information detailed below, it is not possible to determine who, among two or more claimants who have proven that they know the affected wallet’s private key, is the legitimate owner of the tokens.
For this reason, the IOTA Foundation has contracted third-party vendor IDnow to perform identity verifications on the wallet owners. This will help us determine who is the valid owner of the disputed reclaims and return the tokens to their rightful owners.
A list of reclaims that need to go through a “know your customer” (KYC) identity verification process was originally published on 31 December 2017 in the IOTA blog post titled “Claims and Reclaims: Finalization”. You can also scroll down to the end of this blog post to find a link to the most recent list. If your wallet address is part of that list, you will need to go through the identity verification process in order to receive your reclaimed tokens.
To walk you through the process, we have created a simple microsite hosted on the IOTA Foundation’s main website. To initiate the identity verification process, simply go to this microsite and follow the instructions provided.
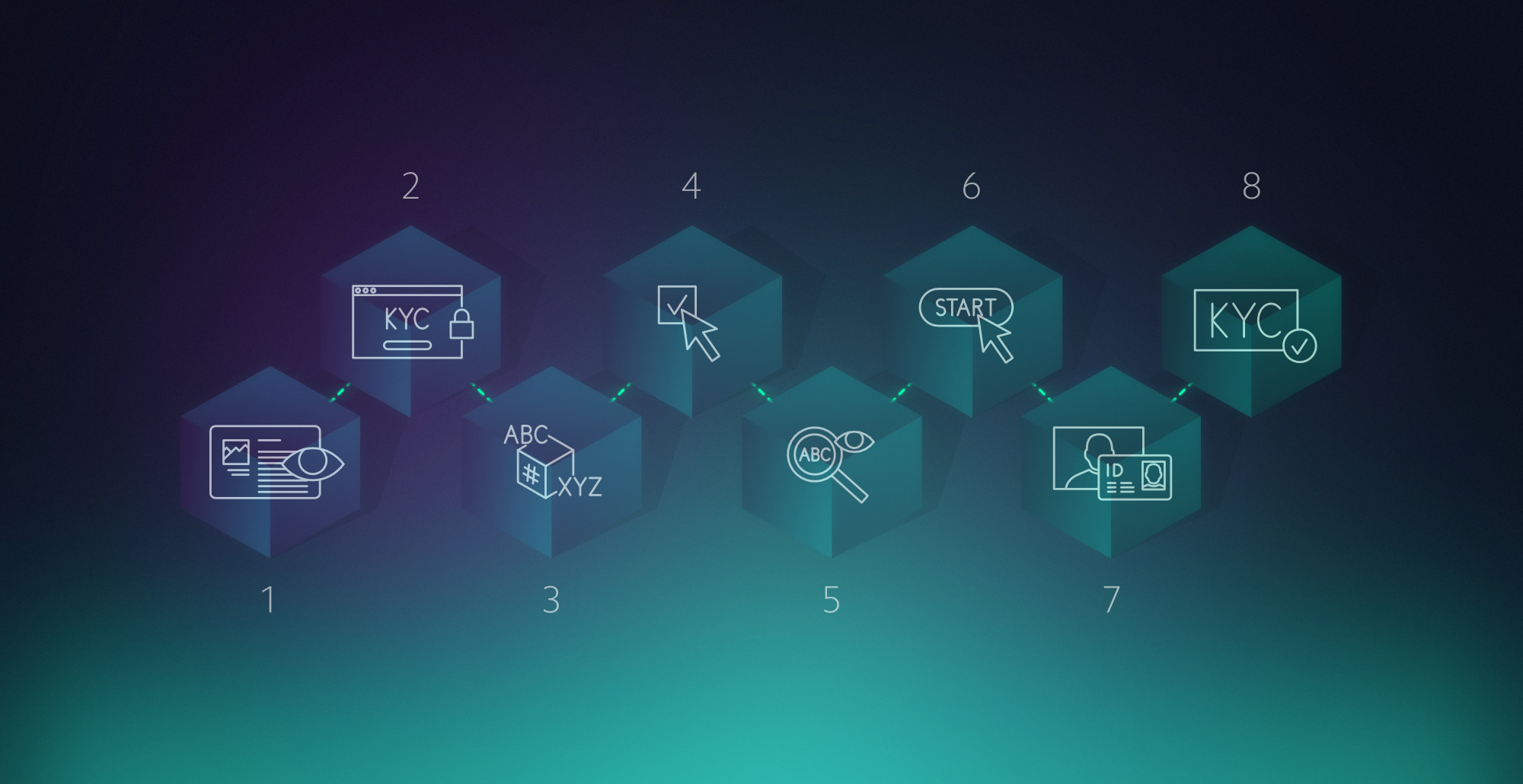
We have designed the process to be as user-friendly and transparent as possible. Here is a step-by-step overview of how it works:
Step 1:Read through this blog post and make sure you understand:
- why your reclaim needs to go through identity verification;
- how to initiate the identity verification process;
- how your data will be collected, used, transmitted, and stored during and after the verification process (see the data protection and data privacy explanations below);
- who you can contact for help if needed.
Step 2: From a secure web browser, go to the website https://kyc.iota.org. For security reasons, you should do this when you are logged onto a network which you know to be safe, for example a password-protected home network. Do NOT use a public WiFi connection or any other shared network where your connection may not be secure.
Step 3: Enter the seed of the IOTA wallet for which you are claiming a refund in the space provided on the web form.* The web app will create a cryptographic hash of your seed as you type it.
* Wait, why is this safe? After all, the IOTA team members are always telling us we should never, ever type our private seeds into random websites!
Very true! You should never, ever type your private seed into a random website or otherwise give it out to anyone whom you do not know and 100% trust, because whoever controls your seed controls your tokens! In this case, however, you have already lost control of your tokens, so you have nothing more to lose. In addition, as explained above, this microsite is hosted by the IOTA Foundation, and it was designed to create a hash of your seed as you type it on your local machine. Your actual seed will not be stored or transferred. Only the hash of your seed will be transferred to IDnow.
Very true! You should never, ever type your private seed into a random website or otherwise give it out to anyone whom you do not know and 100% trust, because whoever controls your seed controls your tokens! In this case, however, you have already lost control of your tokens, so you have nothing more to lose. In addition, as explained above, this microsite is hosted by the IOTA Foundation, and it was designed to create a hash of your seed as you type it on your local machine. Your actual seed will not be stored or transferred. Only the hash of your seed will be transferred to IDnow.
Step 4:Click on the hyperlinked text that says “read more”, which is located to the right of the “I agree” box. This will open up a dialogue box containing essential information about the identity verification process. Once you have read all of the information, close the dialogue box and provide your consent by checking the box that says, “I agree”.
Step 5:Next read through the “disclaimer” section at the bottom of the microsite and double check that you have entered your seed correctly.
Step 6:Click on the button that says: “Start KYC process”. The web app will redirect you to IDnow’s website and will automatically send IDnow the hash of your wallet seed.
Step 7:Follow the instructions provided by IDnow and complete your identification verification as instructed by IDnow’s personnel via video. Note that IDnow will verify your identity in a manner that is compliant with German and EU anti-money-laundering regulations. This means you will need to have a voice and video connection on your device (microphone and web cam), and you will need to have the following information handy when initiating the identity verification process:
- Full name
- Date of birth
- Place of birth
- Nationality
- Street address
- Phone number
- Passport or national ID card
- Piece of paper and pen or pencil
- Device capable of taking a digital photo
Step 8:Once you’ve successfully completed the IDnow identity verification, that’s it! Sit back and relax.
IDnow will send the IOTA Foundation a list of the hashes corresponding to the successfully identified wallet owners and the IOTA Foundation will reach out to these owners to confirm the address to which they would like these tokens to be sent. The IOTA Foundation will initiate the transfer of the reclaimed tokens to the rightful owners of the verified wallets within 30 days of receiving confirmation of successful identification. The major advantages of this process are:
- the IOTA Foundation can have confidence that it is returning the reclaimed tokens to their legitimate owners, since the IDnow identification process greatly reduces the risk of fraudulent reclaims; and
- the rightful owners of the tokens can get their tokens back without ever having to reveal any of their personally identifying information to anyone at the IOTA Foundation.
The reclaim microsite and the IDnow verification process will remain open for 90 days. As noted above, you will receive your reclaimed tokens within 30 days of the IOTA Foundation receiving confirmation from IDnow that your identity has been successfully verified.
It is the IOTA Foundation’s goal to return all reclaimed tokens to their rightful owners. We strongly encourage the legitimate owners of the wallets for which multiple reclaims have been filed to voluntarily submit to this identity verification process so that we can return your tokens to you as quickly as possible. We have done our best to design this process in a way that protects your privacy. In the case of tokens for which no rightful owner steps forward to undergo identity verification, the IOTA Foundation will continue to hold the tokens in safekeeping pending further advice from legal counsel. It is likely that these tokens will at some point be deemed to have been legally forfeited as a matter of law.
IDnow will send the transcripts of all successful identifications — including full identification details — in a secure, encrypted, offline form, to the IOTA Foundation within 30 days of completion of the successful identification. The IOTA Foundation will store these encrypted identification details in a secure, encrypted, offline form for as long as is legally required under applicable German and European anti-money-laundering laws and regulations. The encrypted files will then be destroyed by the IOTA Foundation within 30 days of the end of the legally required retention period. We are currently obtaining legal advice to clarify the period of time for which storage of the encrypted files will be legally required. We will post an update to this blog post as soon as this information becomes available.
The data files corresponding to unsuccessful identifications (aborted identification attempts) will not be transferred to the IOTA Foundation.
For its part, IDnow will destroy its copy of all identification data after a 30-day period following the successful identification or aborted identification attempt. This is in accordance with IDnow’s usual data protection policies.
The IOTA Foundation’s general data privacy policy may be found on its website, at: https://www.iota.org/research/privacy-policy.
IDnow’s data privacy policy may be found at: https://go.idnow.de/privacy/en.
- For assistance with filling out the identity verification reclaim form hosted at the IOTA Foundation microsite https://kyc.iota.org, please contact: [email protected].
- For assistance with IDnow’s identity verification process, please contact IDnow’s support desk at: [email protected].
If you need assistance with a reclaim that does not appear on the identity verification list at the bottom of this blog post, you may contact our reclaim email address for assistance.
We wish to extend our sincerest apologies to all IOTA users who were affected by the October bundle bug. We greatly appreciate your patience and your continued cooperation as we work together to return all tokens to their rightful owners.
https://gist.github.com/th0br0/5b599c813f6edbc684eae40364112461